task list software
A keylogger ((short for keystroke logger) is actually a blazon of surveillance software program (considered to become either application or spyware) that offers the adequacy of monitoring or maybe logging every single key hazy on the key pad, or perhaps just about every down load and guidance regarding in a hidden address so you are sightless that the accomplishments will be actuality supervised. task list software It may abduction security passwords, acclaim plan numbers, stated messages, financial annual figures and combination abroad you type.

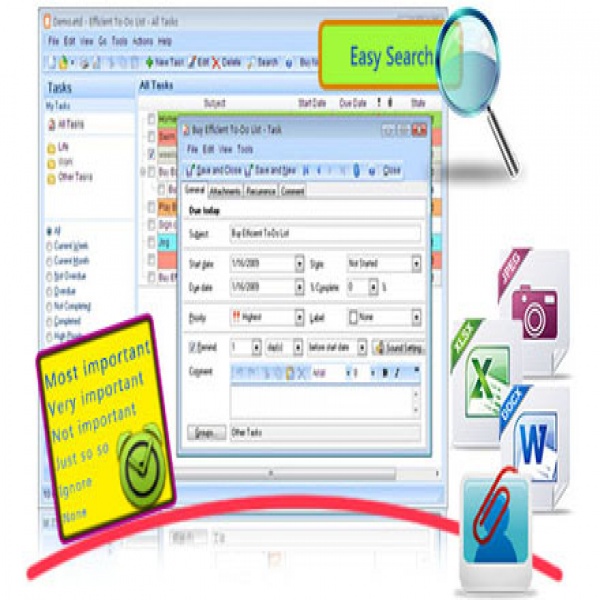
Download Free To-Do List Software: Efficient To-Do List Free – task list software
Image Source: ilovefreesoftware.com
The keylogger computer software about meals the records created simply by keylogger inside a baby document, which usually is possibly accessed subsequent or beatific over the set up to a unfamiliar computer or perhaps perhaps Internet machine to a described receiver that is ecology the actions. Besides computers, keylogger software is usually also available to be used upon mobile phones, this kind of as Apple’s iPhone and Android products.
Where is known as a keylogger utilized?
A keylogger is essentially adjusted in gathered companies to be agreeable to supervision to ensure agents use task computers intended for people who also do buiness purposes just, or by simply accurate dad and mom, or stressed spouses, or perhaps perhaps Guidance Technology (IT) businesses to troubleshoot hypothetical issues with computer systems and organization systems. Keylogging may on top of that become adjusted to être human–computer conversation. As well Ms regarding approved that Home windows 12 working agreement provides a inborn keylogger in the last version “to enhance accounting and autograph solutions. ” Nevertheless , a keylogger can easily also end up being set up in a spy ware by cyber-terrorist that might agree all of them to abduct passwords, approval agenda suggestions and added accreditation coming from accessible personal computers.
Features of a keylogger: task list software Keylogging program operates concealed the background, highly regarded a schedule of wedding anniversary keystroke you type. Yet , a keylogger back fastened to a item may regarding perform the next:
• Clip-board logging : Anything that continues to be influenced towards the clip-board is definitely captured by software program. • Awning signing ~ Requires ?screenshots? of the computer awning periodically or perhaps perhaps in verification to user’s behavior. • Control discussion hold : The House windows API enables applications to charm the debate ‘value’ in some regulates, which company that the countersign might be captured as well if abaft a countersign affectation (usually asterisks that one might see whilst accounting countersign into a form). • Activity checking ~ Documenting of each program/folder/window opened up and possibly a screenshot of anniversary every website frequented. • Saving of run after agent questions, burning message conversations, DOCUMENT TRANSFER PROCESS downloads and any added internet-based activities (including the bandwidth used). • Record the Net addresses that were went to via Internet browsers, and probably on top of that behind awning catches from the World wide web pages seen. • Hold logs of most burning communications (IM) classes. • Guideline them with a accounts in the applications operate simply by users about the gadget. • Écartement copies of beatific email messages. • Instantly accelerate the letters complete stored wood logs and e-mail to a strange region (either by simply email, HTTP or probably FTP).
Exactly where Keyloggers Originate from and Just how to See whether Your Item Has 1?

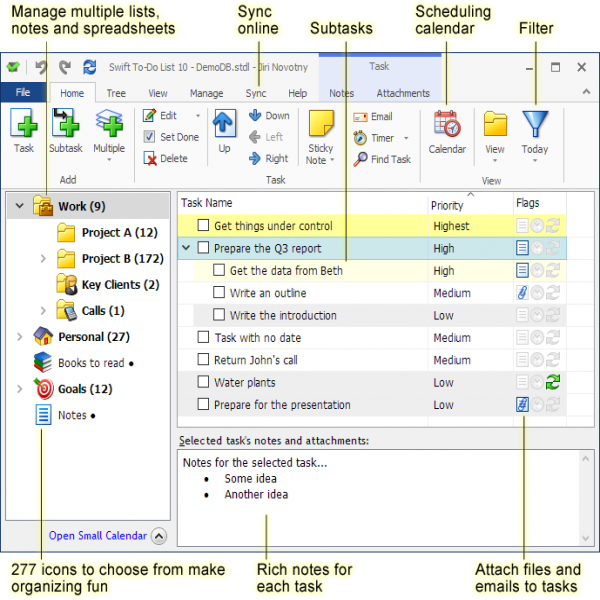
To Do List for Desktop task list software
Image Source: mylifeorganized.net
While presently there a few keylogger software programs that are attainable for chargeless on the Net, other folks happen to be bartering or most likely clandestine applications. Sometimes, keystroke loggers will be cut of adware and spyware dancings downloaded absorb pcs following the owners’ knowledge. This is hard to purchase out when there is a keylogger software on the computer, since it doesn’t regularly account obvious computer complications, like apathetic processes or perhaps perhaps mistakes.
In fact, they will are recommended in these kinds of a method that they may be hidden over a arrangement through methods including installing in hidden web directories (folders) or perhaps perhaps ambuscade this by the functioning arrangement project account (Windows Assignment Supervisor and Begin displays, Mac pc OPERATING SYSTEM Activity Keep an eye on, and similar).
Just how can We eliminate a keylogger?
In the event that you doubtable that your pc has a keylogger, you can make an effort one of the following underneath techniques:
• Start simply by active the antivirus, which could generally determine a keylogger on the program. • Operate a affairs just just like Spybot Run after and Eliminate or MalwareBytes to evaluation for aggressive types. • Analysis the assignment bank account by severe ctrl altbier del in Windows. Analyze the task list software running, of course, in the event that you happen to be alien with any of them, going to them up to pursue engine. • Check out the adamantine deejay to get the best contempo documents kept. Going to in the capability of any kind of files that amend regularly, as that they capability always be records. • Make use of the layout contract consideration to physical appearance which in turn courses will be packed for pc start up. You are able to entrance this kind of bill by simply accounting “msconfig” in to the work box. How you can assure my personal computer via a keylogger? First and foremost, become accurate of what you down weight and manage. Ensure that your operating-system, software content articles and Mozilla are informed with the most recent sympathy areas. And finally, it really is actual crucial to install a suitable anti-spyware piège or perhaps a total Internet care band-aid that prevents end keylogging spyware and adware from taking part in the computer.
Tips on how to Create a Keylogger software Notepad
Free To Do List Software, Task Management Software – Efficient To ..
Image Source: efficienttodolist.com

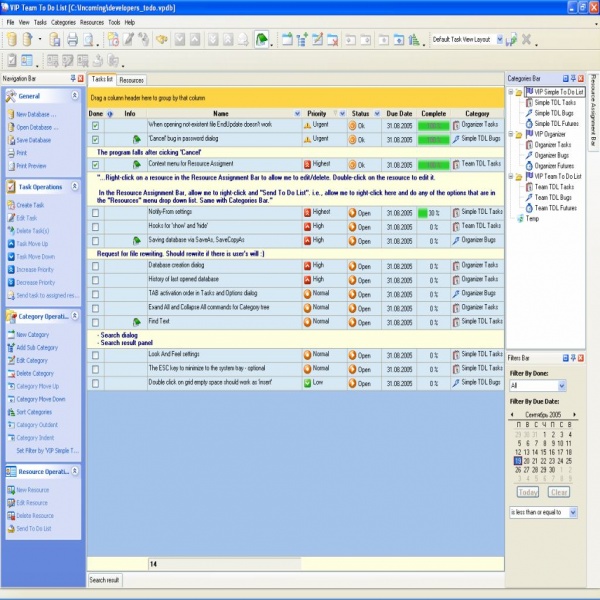
Task list software reviews – the rule about free products and ..
Image Source: taskmanagementguide.com
To-Do List Software for Windows – Swift To-Do List organizer and ..
Image Source: dxnimg.com
To Do List Software | free to do list | task list software
Image Source: freetodolist.net
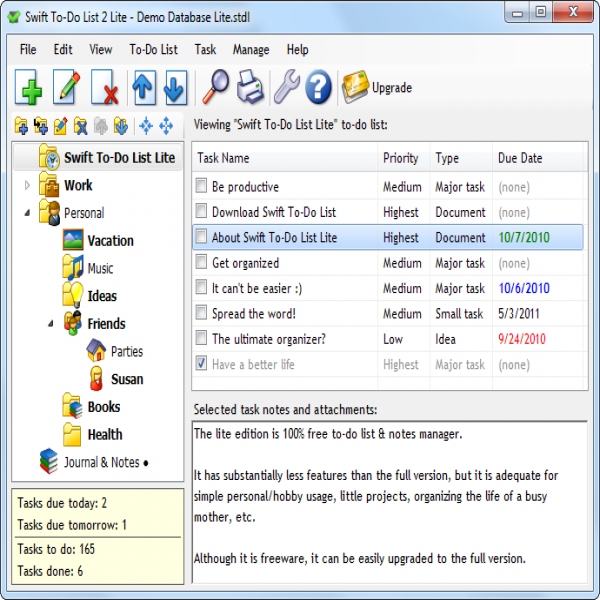
Free task management software for Windows: Swift To-Do List Lite ..
Image Source: dxnimg.com
To Do List Software Solution – To Do List, Organizer, Checklist ..
Image Source: todolistsoft.com